Systems | Development | Analytics | API | Testing
The roadmap to mobile success with Peter-John Welcome
In this podcast episode, we talked to Google Developer Expert Peter-John Welcome about his experience in Android DevOps, the roadmap to mobile success and the steps developers need to take to get there.
Rollbar Academy: Production Code Quality
Node.js Module Exports Explained
As Donald Knuth very wisely put it, computer programming is an art. And an integral aspect of writing clean code and staying true to this art is modularity. This post will cover the use of modules in Node.js — what they are, why they are essential, and how to export and import them in your project. Here’s an outline of what we’ll be covering so you can easily navigate or skip ahead in the post.
How to connect to Ably directly (and why you probably shouldn't) - Part 2
In Part 1 of this two-part series, we walked through how to bypass Ably’s SDKs and connect to Ably’s backend using websocat, where every JSON message has to be typed out by hand. In this second part, we’ll fix that tedious bit by switching to NodeJS, and we’ll continue our process of building our own minimal Ably (NodeJS) SDK.
An Introduction to Metaprogramming in Elixir
In this world, there are many mysteries — but few are as elusive as metaprogramming in Elixir. In this four-part series, we’ll start by looking at core concepts and then explore how metaprogramming operates in Elixir specifically. Let’s develop an understanding of metaprogramming and uncover some Elixir metaprogramming secrets!
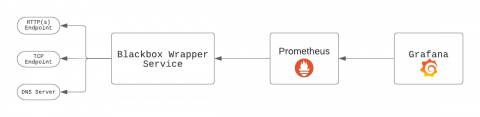
Build an Uptime Monitoring System in Ruby with GCE, Cloud Storage, and PubSub
Google Cloud Platform provides developers with many tools to build scalable apps in a way friendlier than AWS. In this article, Olasubomi Oluwalana shows us how we can use the Google Cloud Engine, Storage, and PubSub offerings to build an uptime monitoring system in Ruby.
Perfecto | Verified Steps on Bitrise
Top 10 Tools For Google Cloud Architect
Google Cloud Platform is a complex suite of services that are aimed at satisfying client’s computing, storaging, and application operating needs. App Engine, Cloud SQL, Cloud Speech API, Deployment Manager ( just a share of ) are the proud services of a GCP. All of them are developed for optimizing business and making business-client relationships easy and comfortable for sealing the deals and conversions go high.
9 Best Practices for Application Logging that You Must Know
Have you ever glanced at your logs and wondered why they don't make sense? Perhaps you've misused your log levels, and now every log is labelled "Error." Alternatively, your logs may fail to provide clear information about what went wrong, or they may divulge valuable data that hackers may exploit. It is possible to resolve these issues!!!